Numa Incident Analysis
Incident Summary
On 10 August 2025 Numa protocol was exploited for ~$313k. A malicious actor acquired additional Numa tokens by liquidating victim accounts after manipulating the NumaVault by minting nuBTC. Minting the nuBTC inflated the total synth value and in turn, reduced the collateral value of cNuma according to the Numa VaultManager logic.

Vulnerability
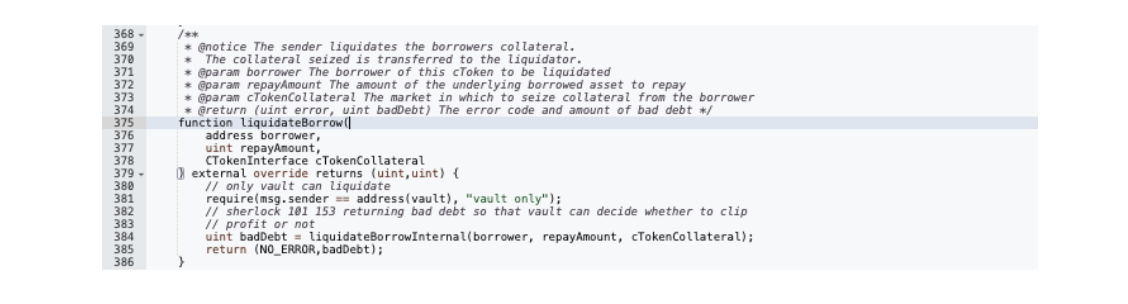
Much of Numa borrowing and lending logic is forked from Compound where the NumaComptroller checks account collateral status before borrow/liquidation to prevent bad debt.
In cases where a hypothetical shortfall is computed in vars.sumBorrowPlusEffects -vars.sumCollateralNoCollateralFactor within getHypotheticalAccountLiquidityIsolateInternal(),
 the collateral value is calculated as cTokenBalance*(exchangeRate*oraclePriceCollateral).
the collateral value is calculated as cTokenBalance*(exchangeRate*oraclePriceCollateral).
 The logic, which is forked from Compound, is standard practice for lending pools to ensure liquidity.
The logic, which is forked from Compound, is standard practice for lending pools to ensure liquidity.
The vulnerability comes from the volatility of cNuma, which, according to the whitepaper is “a non-liquidatable, leveraged-long on a given liquid-staking token“. It's price as collateral is affected by several balances in the protocol and can be manipulated.
The collateral price is fetched by NumaVault.numaToLst() as tokenAmount*sellFee
 where tokenAmount is calculated by VaultManager.numaToToken() as (EthBalance - synthValueInEth) / circulatingNuma. EthBalance is the total value available in all vaults at 1,499,561(,701,917,513,022,952,959).
Initially, synthValueInEth, representing all synthetic nuTokens minted, was at 160,092(,928,178,718,414,075,940).
where tokenAmount is calculated by VaultManager.numaToToken() as (EthBalance - synthValueInEth) / circulatingNuma. EthBalance is the total value available in all vaults at 1,499,561(,701,917,513,022,952,959).
Initially, synthValueInEth, representing all synthetic nuTokens minted, was at 160,092(,928,178,718,414,075,940).
After minting 3.08 nuBTC with flash loaned Num, the total SynthValueEth was at 1,351,479,(760,017,807,443,024,894), where the majority came from the newly synthesized nuBTC.
 The resulting collateral price was greatly reduced, leaving victim accounts liquidatable.
The resulting collateral price was greatly reduced, leaving victim accounts liquidatable.
Key Transactions
- https://sonicscan.org/tx/0x56abdbc84232658617853f233f52e6b4c855129c7ab163a588c2bac62ea30408
- https://sonicscan.org/tx/0x230467308679169c3cb6966b43759ba53d1ee856b4148ff936f8f8638353a710
- https://sonicscan.org/tx/0x916fc5e65eec759979529336522fe7c83a346b5a91d7ac6b6f0a748a3b36eb30
Attack Flow
Addresses
Exploiter:
- Wallet: 0xEf1df44E122872d0feF75644AFc63a5C35F97674
- Contract:
- 0xd4de62a8DD0F0D43ca8886E0393e159D5E5e38e6
- 0x3041652a157fd9230eda8e741c103e4688a37c05
- 0x301EB95463D4f1336Ed01F59EC794767D4C8Cc32
- 0x077165c03c17b80fb75e094674471f13c7882a28
Numa:
- CToken: 0x16d4b53de6aba4b68480c7a3b6711df25fcb12d7
- CNumaLst: 0xb2a43445b97cd6a179033788d763b8d0c0487e36
- Vault: 0xde76288c3b977776400fe44fe851bbe2313f1806
- VaultManager: 0xf8021C37b20a0C5BaD67b67Cc79Dd98e7eF82f6B
- Comptroller: 0x71e20a7d3f4ead75f603b11e5fbd2cc71f28d0dc
- NumaPriceOracleNew: 0xa92025d87128c1e2Dcc0A08AFbC945547Ca3B084
Step by Step
Attack flow based on transaction hash 0x56abdbc84232658617853f233f52e6b4c855129c7ab163a588c2bac62ea30408
- Flashloan 1.2M stS (Beets Staked Sonic token ; ~$3/stS) from Beets Vault and ~120K Numa tokens from several Rameses Pools.

- Mint ~960K cNUMA with 19.2K Numa tokens at exchange rate of 2e26,
then borrow ~138K Beets Staked Sonic tokens on CNumaLst.
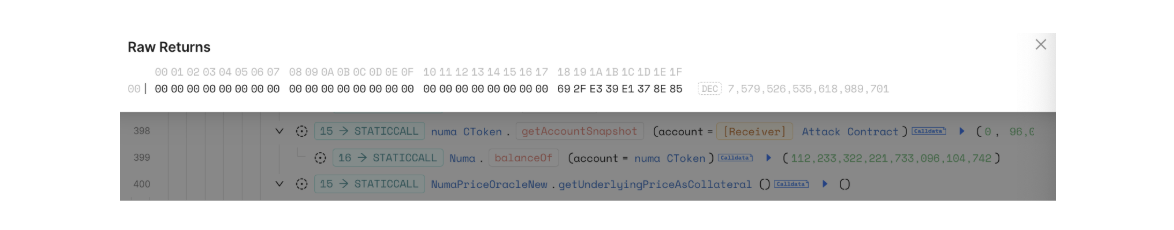
The cNUMA price is at 7,579,526,535,618,989,701 (7.579e18).
- Call NumaPrinter to mint 3.08 nuBTC with the remaining 100.8K Numa (98.3K Numa burned and 2.5K Numa transferred from attacker).
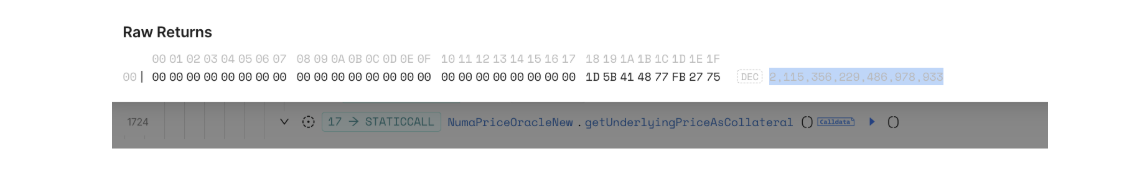
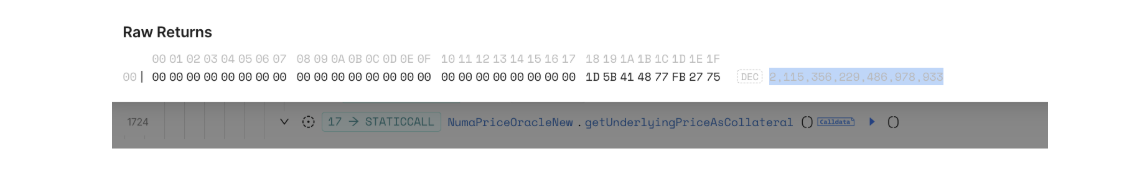
 The minting greatly inflated the total synth value and in turn, reduced the collateral price of cNuma, which is now at 2,115,356,229,486,978,933 (2.115e18).
The minting greatly inflated the total synth value and in turn, reduced the collateral price of cNuma, which is now at 2,115,356,229,486,978,933 (2.115e18).
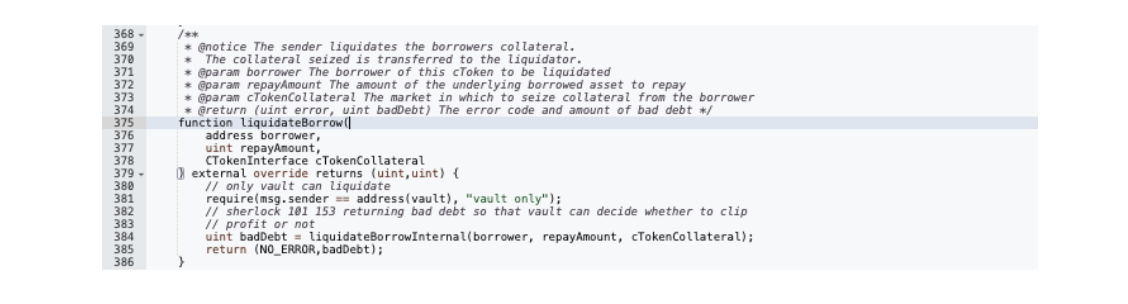
- Transfer all 1.338M stS to attack contract 2 which liquidated a series of Lst borrower accounts.
 Liquidate borrowers and seize the following:
Liquidate borrowers and seize the following:
- 3.5K Numa with 7.3K stS from 0x6B9d3797d0c1Ee9824acBE456365cF02b5B87d5E
- 8.9K Numa with 18.5K stS from 0x2F9A0BB9a50C85B1163B70B6cdf437881892F4CF
- 3.3K Numa with 6.9K stS from 0x2C7F65dFaa81117E759792267e156D7E0759fC8e
- 23.8K Numa with 49.3K stS from 0x6122861A8Cc736d98caD0506df5d0618429cF490
- 19.2K Numa with 39.8K stS from 0xd4de62a8DD0F0D43ca8886E0393e159D5E5e38e6 (attack contract itself)
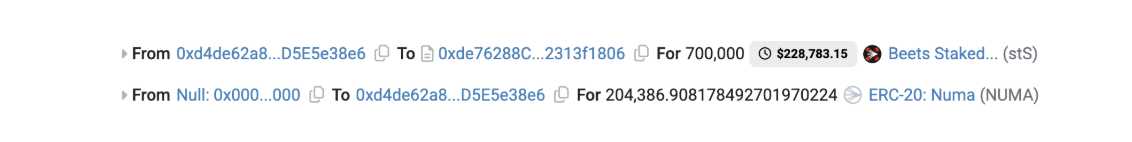
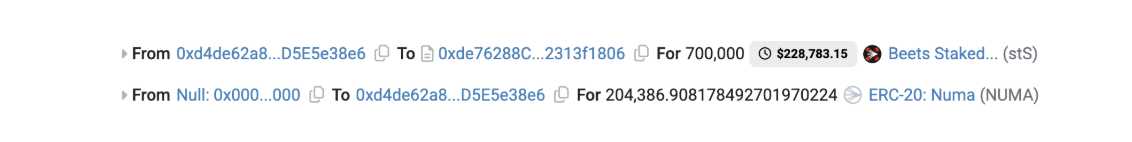
- Buy 204.3K Numa with 700K stS and burn 3.09 nuBTC to acquire 88.1K Numa.
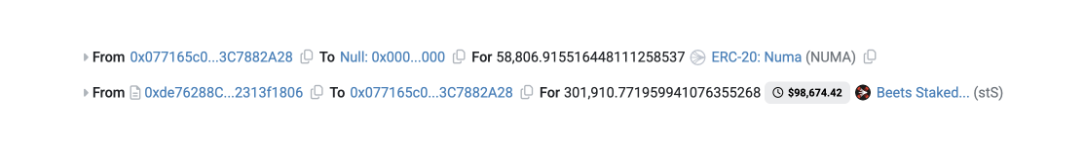
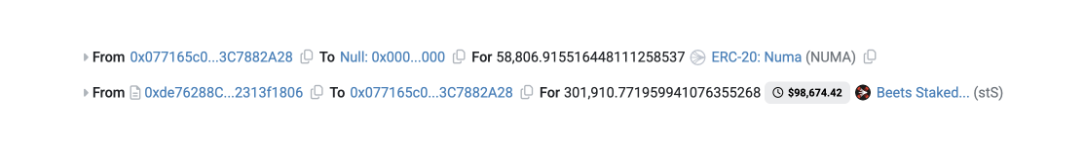
 Then sell 58.8K Numa acquired from liquidation for 301.9K stS.
Then sell 58.8K Numa acquired from liquidation for 301.9K stS.
 Finally, repay the flashloan.
Finally, repay the flashloan.
Fund Flow
In total ~973k stS was swapped and bridged from Sonic to Ethereum network.

0xEf1df44E122872d0feF75644AFc63a5C35F97674 bridged 74.3 ETH (~$313K) over five transactions.
 A few minutes after, 74.2 ETH was deposited into Tornado Cash.
A few minutes after, 74.2 ETH was deposited into Tornado Cash.
 To keep up to date on the latest incident alerts and statistics follow @certikalert on X, or read our latest analysis on certik.com.
To keep up to date on the latest incident alerts and statistics follow @certikalert on X, or read our latest analysis on certik.com.

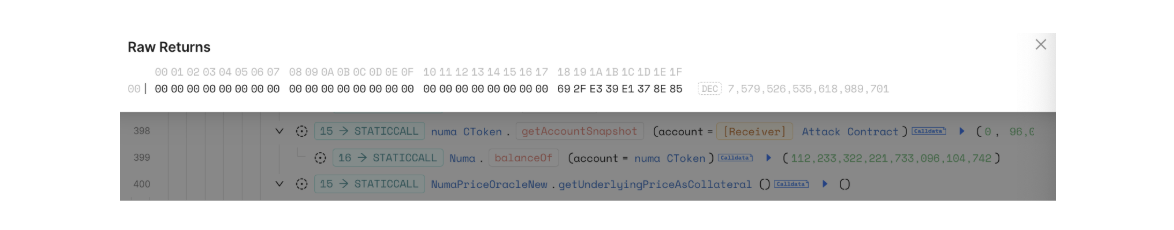
 The minting greatly inflated the total synth value and in turn, reduced the collateral price of cNuma, which is now at 2,115,356,229,486,978,933 (2.115e18).
The minting greatly inflated the total synth value and in turn, reduced the collateral price of cNuma, which is now at 2,115,356,229,486,978,933 (2.115e18).
 Liquidate borrowers and seize the following:
Liquidate borrowers and seize the following:
 Then sell 58.8K Numa acquired from liquidation for 301.9K stS.
Then sell 58.8K Numa acquired from liquidation for 301.9K stS.
 Finally, repay the flashloan.
Finally, repay the flashloan.